Monitoring & Management
Tell you what you don't know
- Home
- »
- Services
- »
- Technology Services
- »
- Monitoring & Management
Proactive Monitoring & Management
Almost every hardware failure starts with a minor problem that goes unnoticed. After a failure a technician go through the logs to understand what the cause of the failure was. This often leads to a root cause that if avoided or repaired quickly the resulting failure could have been avoided. This is the purpose of the tools that we have used internally and are now offering to our customers. Mirrored Storage offers these on workstations and servers that include both Anti-Virus and Anti-Malware.
Problems that are easy to identify and fix:
- Presence or exposure to a virus
- Failed or failing components such as memory or disk
- Operating System patch being behind on required/highly recommended by the manufacturer
-
Excessive resources being used range from a virus running in the back ground, streaming media, etc.
- Third party software patches
- -
Server monitoring
- SNMP & network monitoring
- Workstations monitoring
- VM monitoring - - Application Control - Active Directory Users Query; Running Process
- Clean-Up - Clean Temp Log Files; Clear Event Log; Defragmentation
- Exchange - Large Mailboxes; Exchange Store Control
- Windows - Reboot; Service Control - - A complete suite of patch management tools in one application
- Provides support for many popular applications
- Assure software in place to maintain a secure, compliant network
- Upgrade to the latest software versions, automatically
- Easily deploy patches network-wide - - Manipulate the file system (move, copy and delete files)
- Map network drives, edit the registry, install software
- View running processes and the resources they’re using, kill non-responsive processes and add a process check to monitor problem processes
- Start, stop and restart services
- Change the start-up type of a particular service
- Show service dependencies and Windows Service Check to monitor problem services - - Automatically gather information from any device with the MAX agent installed
- Free reports on hardware, software and software licenses
- View configuration information
- Prepare comprehensive inventory and asset management and tracking reports and track any changes and Track software license compliance
- Audit software and hardware changes and confirm expected state is actual state
- Access detailed hardware and software information on your Dashboard anytime, anywhere – right down to serial numbers, software versions, processor type, memory, and more
- Cut admin effort with custom fields for asset numbers, installation dates, warranty dates, care pack details or any other information you need
- Spot banned software and take action before it causes problems
- Provide customers with detailed inventory reports - - Daily and weekly – fixed content that quickly demonstrates daily health checks – in an easy to follow graphic format.
- Monthly – customizable content to who ongoing issues and demonstrate cases for additional system investments. - - Enable on individual servers and workstations or on all servers and workstations at a client or site
- Configure every aspect of the Managed Antivirus agent including scan schedules and remediation action
- Fine tune protection policies
- Manage quarantine
- Free malware removal service
- Used on over tens of thousands of networks worldwide
- Flexible reporting capabilities - - Block users from visiting suspected and confirmed unsafe sites
- Apply web filtering to enforce internet access policies in the workplace
- Set white lists and black lists to override category based filters
- Optionally apply a schedule so employees can access non-work sites during out of office hours or on the lunch hour
- Apply a 'web bandwidth' check and be alerted when there’s excessive bandwidth activity on a network
- Intelligently filter internet activity by day, category and URL to reveal trends, spikes and irregularities and show or hide URL data depending on data privacy requirements
Again, we do the implementation and continuous monitoring for you. Many things are automated, or we can make changes remotely automatically. We can also remotely connect to your computer to help you with issues as they arise.
Detail Package Component Items INCLUDED in BASE MIRRORED STORAGE offering
| Component | Description |
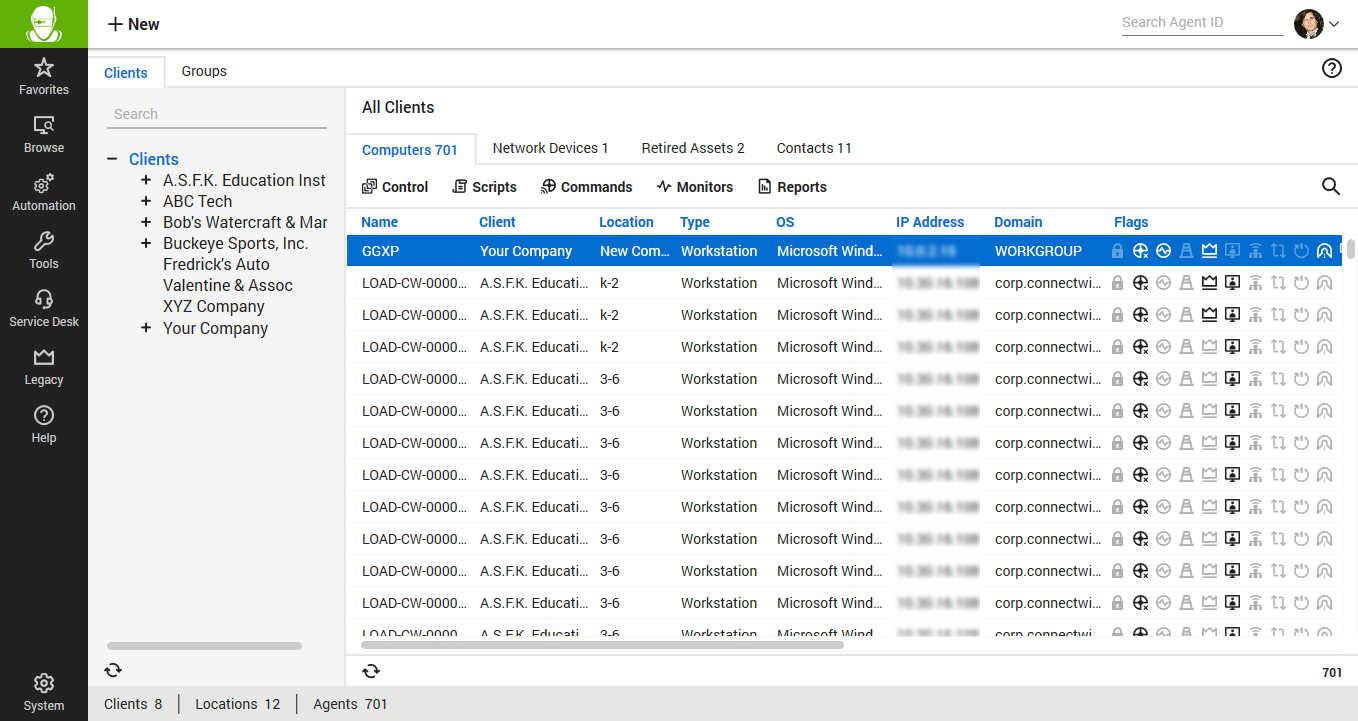
| Remote Monitoring | Real-time info on system status you get to stop small problems in their tracks before they become expensive disasters. |
| Automated Maintenance | Schedule or order running of traditional maintenance tasks. |
| Patch Management | Scan networks automatically or on demand and install and manage patches on all machines, across different operating systems |
| Remote Access | Take advantage of 24/7 remote IT support so you don't need somebody there at the other end. Streamline your teams’ activities and provide a hassle-free support experience with the Remote Background Management (RBM) tool - a tool which enables you to work on client machines remotely to fix problems without interrupting the end-user. |
| Asset and Inventory Tracking | Network inventory and asset tracking capabilities help manage them easily and effortlessly. |
| Reporting | Produce reports automatically and as requested. Such as: |
| Managed AntiVirus & AntiMalware | Total Protection includes multiple solutions. The first two are AntiVirus and AntiMalware. |
Detail Package Component Items AVAILABLE IN MIRRORED STORAGE offering
| Component | Description |
| Web Protection | The Web Protection feature is built around a policy-driven approach so each device that you turn on for Web Protection will point to a central policy. You can edit the policy and adjust settings for the devices with that particular policy, helping you to scale Web Protection to a range of devices as opposed to having device-level settings across the board |
| Cloud Storage | The Cloud is being used by more and more businesses and individuals. The leading concerns around security and privacy, as well as regulatory requirements, are leading many to look for a better solution than offerings that utilize public storage.
- Online storage access for PCs, Macs, File Servers, Web Browsers, and Mobile Devices - Access, share, restrict and auditability of every file or folder access - Get your data where and when you need it from iOS, Android and Windows with native clients and from any browser |
